Most employees use AI daily—but few are trained. That gap creates hesitation and mistakes. Here’s how to build real AI confidence with support and guardrails…
By Content Type
How to make your team AI-confident
Most employees use AI at work—but many stay quiet, fearing judgment. Build confidence with culture, training, and clear rules so AI becomes a partner…
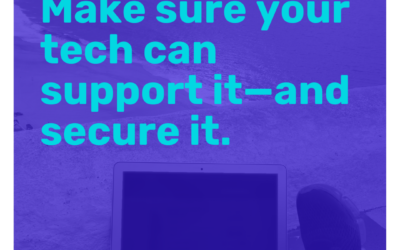
Chicago Remote-Ready Insurance Hiring: A Secure Tech Stack Guide
Hiring remote insurance talent in Chicago? Your tech stack can speed onboarding—or create risk. Build the Remote-Ready 7 before you scale…
Spam Isn’t Just Annoying Anymore: The Inbox Threat You Can’t Ignore
Spam now looks like invoices, delivery notices, even coworkers. One click can steal passwords or trigger fraud. Here’s how to stop it before it lands…
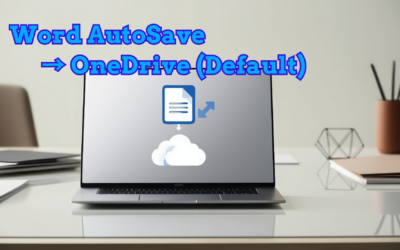
Word’s New Default: AutoSave to OneDrive (And What It Means for You)
Word now saves new docs to OneDrive by default—so crashes don’t erase hours of work. Prefer local-only files? Here’s what to check before you agree…
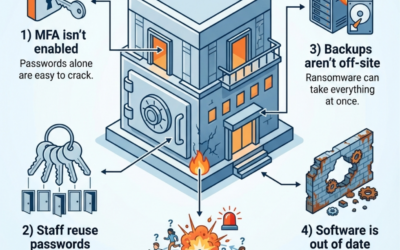
5 Clues your business looks like an easy cyber target
Think you’re too small to be hacked? Missing MFA, reused passwords, no off-site backups, old software, and no breach plan can paint a target. See how to fix…
Never lose a Word document again
Word’s new default AutoSave sends new docs to OneDrive—great for backups, tricky for privacy and control. Love it or hate it, it’s changing how you work…
Copilot is starting to act like a “universal remote” for Microsoft and Google
Copilot is becoming a universal remote for Gmail + Outlook. Fewer tabs, fewer double-books, faster docs and decks. The big question is trust…
One assistant for Outlook, Gmail, and Calendar
Copilot now connects Outlook, Gmail, and Google Calendar in Windows—so you can get answers fast without switching tabs. Here’s what it can do for you…
Build Smarter with Power Platform
Build apps, automate workflows & surface insights fast with Microsoft Power Platform—Reintivity’s low-code experts turn ideas into scalable solutions. Get started…
Spam isn’t “just spam” anymore Cybersecurity Guide
Spam isn’t noise anymore—it’s a delivery system for phishing, malware, and fraud. Learn the simple layers that block most attacks before they reach your inbox…
The Skeptical Leader’s IT Partner Playbook
Your IT shouldn’t feel like a mystery or a constant fire drill. Here’s how to spot real partnership, reduce risk, and build a roadmap that actually works…
Are You Getting Real IT Partnership—or Just Tech Support
Tech is how your organization runs now—not just what it runs on. Learn how to spot real IT partnership, reduce risk, and build a roadmap that scales…
Preview: AI audio translation in Microsoft Edge
Microsoft Edge is testing AI that translates video audio in real time, turning foreign-language training and updates into instant insights. See how it could…
AI live audio translation is coming to Microsoft Edge
AI-powered audio translation in Microsoft Edge could turn global videos into instant training and insights for your team. See how it works (and its limits)…
“I’d Never Fall for That.” Famous Last Words in Healthcare Email Security
Think your team would never click a bad link? In busy clinics, one rushed email can expose patient data and halt care. See how to turn staff into…
Now live: You’re in charge of what Copilot remembers
You choose what Microsoft Copilot remembers, what it forgets, and how personally it supports your work. Take control of your AI assistant and discover how it can…
New in Copilot: You’re in charge of what it remembers
Copilot just got a memory upgrade—so your AI can remember clients, formats, and preferences while you stay in control. See how it works for your team…
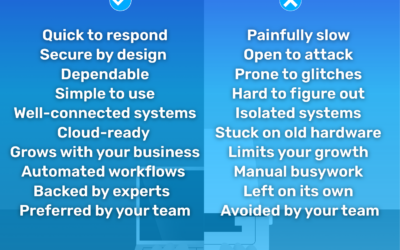
From Tech Frustration to Workflow Flow
Clunky tech turns simple work into a slog. The right systems boost security, connection, and morale. Often, all it takes is a few smart changes…
Don’t Be Fooled by Fake Apps: Hidden Malware Threats to Your Business
Cybercriminals hide malware inside fake apps that look real. Even careful staff can be fooled, putting your business at risk. See how to protect…
Watch out for fake apps hiding malware
Fake look-alike apps are tricking staff and slipping malware onto work devices. Learn how to spot the red flags before your data is exposed…
Layered Security: Why One Tool Is Never Enough
Cybersecurity isn’t one magic tool. Real protection comes from stacked layers that catch what others miss. The real question is how many layers you have…
Old School Tech, New School Threats: How “Retired” Devices Put K–12 Data at Risk
Your old school laptops aren’t just clutter. Without proper wiping, they can leak student records and staff data. Discover how a simple device plan can…
AI vs. AI: Inside the Next Wave of Cybercrime
AI is supercharging cyberattacks—and rewriting the rules of defense. Discover how AI-driven malware works and what your business must do next…
Managed Software Technology Services
Reintivity’s Managed Software Technology Services bring proactive maintenance, patching & real-time monitoring—turning IT from reactive cost to strategic asset. Find out how…
When 4 Out of 5 Cyberattacks Are Run by AI
4 out of 5 cyberattacks now use AI, hitting SMBs at machine speed. See how to fight back with layered defenses before attackers get smarter…
Windows 11 Is Finally Fixing Dictation Headaches
Tired of fixing messy dictation errors? A new Windows 11 feature promises smoother, smarter, more accurate voice typing so you can finally say goodbye to…
Goodbye Clunky Transcripts: Meet Fluid Dictation in Windows 11
Windows 11’s new Fluid Dictation uses AI to clean up “umms,” punctuation, and grammar so your Chicago team can talk, not type. See how it changes everyday work…
Is Your Business Finally Ready for the Cloud?
Learn how public, private, and hybrid cloud options secure your data, reduce IT hassles, and boost collaboration. See which approach is right for your business…
Cloud-Ready: A Practical Guide to Future-Proofing Your Organization
From file cabinets to cloud apps, the way we work has changed—but has your tech kept up? See how to cut risk, boost resilience, and get cloud-ready…