Managed Services
Software & IT Support
Since 2013 we’ve worked with evolving businesses and understand how you have unique challenges and technical support does not have to be one of them! We know that there are 1000s of IT and software support companies all offering the best solution, but we really believe that we provide an IT and software support contract like no other.
Service Areas
Frankfort, IL
21201 S Elsner Rd
Address
Chicago, IL 60605
-
21201 S Elsner Rd, #1094,
Frankfort, IL 60423
Contact Us
Hours of Operation
Mon - Fri:
9 AM - 5 PM
-
Sat - Sun:
By Appointment
IT & Software Support
Software & IT Support
Cloud Application Support
Web Hosting & Domain Management
Managed Licenses
A variety of IT support services offered by trained professionals with quick on-site response.
We recognize that the unexpected occurs from time to time, and you require assistance in resolving IT difficulties. All of our managed IT services are supported by our Service Desk, which is ready to help you anytime you need it.
Our Service Desk is built on the ITIL framework and manned by highly experienced engineers, so we can respond and resolve IT support problems fast. It is backed by a Service Level Agreement that guarantees response times.
Cloud Office Tools
Modern Workplace applications makes it easier for remote and virtual teams to create documents, presentations, meetings, calendar invitations, spreadsheets, and more, with management of access and sharing controls for improved collaboration and security.
Organizations are increasingly moving their technology workloads to the Cloud, citing numerous advantages such as increased agility, lower consumption-based costs, ease of scaling to meet market and geographic demands, product and service transformation, internal operations optimization, and improved digital customer engagement.

Social Messaging for Teams
Cloud Storage
Cloud Directory
Email Client Configuration

Social Messaging for Teams
Cloud Storage
Cloud Directory
Email Client Configuration
Modern Workplace applications makes it easier for remote and virtual teams to create documents, presentations, meetings, calendar invitations, spreadsheets, and more, with management of access and sharing controls for improved collaboration and security.
Organizations are increasingly moving their technology workloads to the Cloud, citing numerous advantages such as increased agility, lower consumption-based costs, ease of scaling to meet market and geographic demands, product and service transformation, internal operations optimization, and improved digital customer engagement.
Maintenance & Updates

No-nonsense, jargon-free support

Website Maintenance
Cloud Computing Platforms
Disaster Recovery
The cloud is where collaboration thrives, from mobility that allows you to work safely from anywhere to flexible storage solutions that keep everything in one place. You are fortunate in that we are the place where the best cloud productivity solutions meet the best migration methods.
Moving server workloads to Microsoft Azure or Amazon Web Services (AWS) allows organizations to benefit from lower costs & enhanced security, resilience & agility.
Organizations can also build Cloud-native software on these platforms to create competitive advantage through lower server administration, reduced costs and with access to cutting-edge AI, automation & analytics.
Cybersecurity
Discover comprehensive cybersecurity services designed to protect your business around the clock. From meticulous cybersecurity assessments that pinpoint vulnerabilities to advanced, multi-layered security solutions tailored to your specific needs, we offer the protection you require.
Navigating the complex landscape of regulatory requirements is challenging but crucial for maintaining trust and legal compliance. Reintivity's Cybersecurity Compliance service ensures that your business meets all relevant legal, regulatory, and industry standards, such as GDPR, HIPAA, and PCI-DSS.
24/7 Monitoring and Response
Cybersecurity Compliance
Cybersecurity Assessment
Data Encryption and Multi-Factor Authentication
24/7 Monitoring and Response
Cybersecurity Compliance
Discover comprehensive cybersecurity services designed to protect your business around the clock. From meticulous cybersecurity assessments that pinpoint vulnerabilities to advanced, multi-layered security solutions tailored to your specific needs, we offer the protection you require.
Navigating the complex landscape of regulatory requirements is challenging but crucial for maintaining trust and legal compliance. Reintivity's Cybersecurity Compliance service ensures that your business meets all relevant legal, regulatory, and industry standards, such as GDPR, HIPAA, and PCI-DSS.
Solving your industry IT challenges
Healthcare
Our largest industry reach. We specialize in healthcare data processes.
Education
Our custom and standard services are aimed at clients that demand quality.
Government
Meet regulatory requirements and ensure continuous tech integrity.
Non-profit
IT support for organizations that are the heart and soul of many communities.
Insurance
Delivering tailored software solutions that improve insurance services.
Why Outsource?
- You have limited internal resources.
- Cost-effective access to expertise.
- Off-load cloud, software & technology management.
- Cost-effective, fixed monthly costs.
- Clear reporting, insights and forecasting.
- Met Service Levels.
- Allows you to focus on business growth.
- Improves ROI on IT investments.
- Simplified digital transformation.
- Mitigates growing SMB cyber security challenges.
- Prevents costly downtime.
- Better business continuity.
- Peace of Mind.

Already outsourcing? How to switch if you’re not satisfied...
If your current provider is not giving you the right level of service and support, you can’t afford to wait: choose a partner that is flexible, friendly and focused on what your business needs to drive continuous growth.
We will take care of the switching process and provide a dedicated Cloud & IT Service Expert to work with you every step of the way.
While we like to share the newest innovations in cloud, software and technology, we’ll never try to sell you something you don’t need.
Solving your Business IT Challenges
Productivity
Are you working harder or smarter?
Technology
Is your software technology aligned to your business goals?
Data
Does your data help you make smarter business decisions?
Operations
Is your IT and software providing you with stability & mobility?
People
Do you have the right IT people? Are they empowered by your IT?
Frequently Asked Questions
What’s included in Managed Services, and what counts as project work?
Managed Services covers day-to-day support, maintenance, monitoring, and keeping systems stable. Project work is bigger change: migrations, major upgrades, new systems, or redesigns. We’ll be clear up front so you’re not guessing what is covered.
Do you support both cloud apps and on-prem environments?
Yes. We support cloud productivity tools and cloud infrastructure, and we also support on-prem needs where they still make sense for the business. Many clients run a mix, and we help you manage that without complexity.
Can you support us if we already have in-house IT (co-managed IT)?
Yes. We can take the day-to-day workload off your internal team, cover after-hours monitoring if needed, or handle specialized areas like security and backup. We align on roles and escalation so nothing falls between the cracks.
What size organizations are the best fit for your support model?
We’re a strong fit for teams that rely heavily on technology but do not want technology management to consume leadership time. If you have recurring issues, growing security requirements, or a mix of vendors and systems, Managed Services brings structure and consistency.
Which industries do you support most often?
We commonly support healthcare, education, government, nonprofit, and insurance organizations. Each of these comes with practical security and compliance needs, so we plan support with that reality in mind.
Show more
How do we request support, and what happens after we submit a ticket?
You can request support through the Service Desk and the support portal. Once a request is submitted, it is triaged, assigned, and tracked through to resolution with clear communication along the way.
What are your hours of operation? Do you offer after-hours coverage?
Standard hours are Monday through Friday, 9 AM to 5 PM, with weekends by appointment. If you need around-the-clock monitoring and response for security, we can provide that as part of the security stack.
Do you offer an SLA, and what response times can we expect?
Yes. Our Service Desk is backed by a Service Level Agreement, and response targets are typically based on severity so urgent issues move first. We’ll review the SLA with you so expectations are written down.
When do you go on-site versus fixing issues remotely?
Most issues are handled remotely because it is faster and is the typical approach across the IT support market. On-site visits happen when physical access is required (hardware, cabling, network gear, device swaps), or when an in-person visit will shorten downtime. Many organizations also choose planned in-person check-ins weekly or monthly for physical checkpoint reviews, strategy coordination, and stakeholder alignment, even when day-to-day support stays remote.
Who will we work with day-to-day, and how is escalation handled?
You’ll work with the Service Desk for day-to-day requests, and issues escalate to more senior engineers when needed. Many organizations also choose a dedicated account manager as their first-line contact, someone who stays closely familiar with your environment, priorities, stakeholders, and recurring pain points. That way, you get faster context, clearer coordination, and fewer “re-explain it from scratch” moments when something is urgent or cross-functional.
Show more
What security controls are included?
We support layered security including assessments, encryption, multi-factor authentication, and compliance-focused controls. We also offer 24/7 monitoring and response so threats are detected and handled quickly.
What does “24/7 monitoring and response” mean in plain English?
It means key systems and security signals are watched continuously, and alerts trigger action based on agreed priorities. We define what is monitored, how incidents are handled, and who gets notified.
How do you handle backup and disaster recovery? Do you test restores?
Disaster recovery is part of our support coverage, and we help design backup and recovery so you can restore what matters when something breaks. We strongly recommend routine restore tests, because a backup that cannot be restored is just a file.
Can you help with compliance requirements like HIPAA or PCI-DSS?
Yes. We support cybersecurity compliance aligned to common regulatory and industry standards such as HIPAA, SOC2, NIST CSF, NIST RMF and PCI-DSS. We focus on practical controls and documentation that stands up to real oversight.
If we are switching providers, what does the transition look like?
We handle the switching process with a structured onboarding plan, so service stays stable while we take over. We also coordinate directly with your current IT firm to support a clean handoff, gather the right documentation and access, and reduce the risk of downtime or missed details. The goal is minimal disruption, clear ownership, and no surprise gaps in support or security.
Share Your IT Support Need
Share a few details about your software & IT support need and one of our managed services experts will contact you.
Lastest Resources
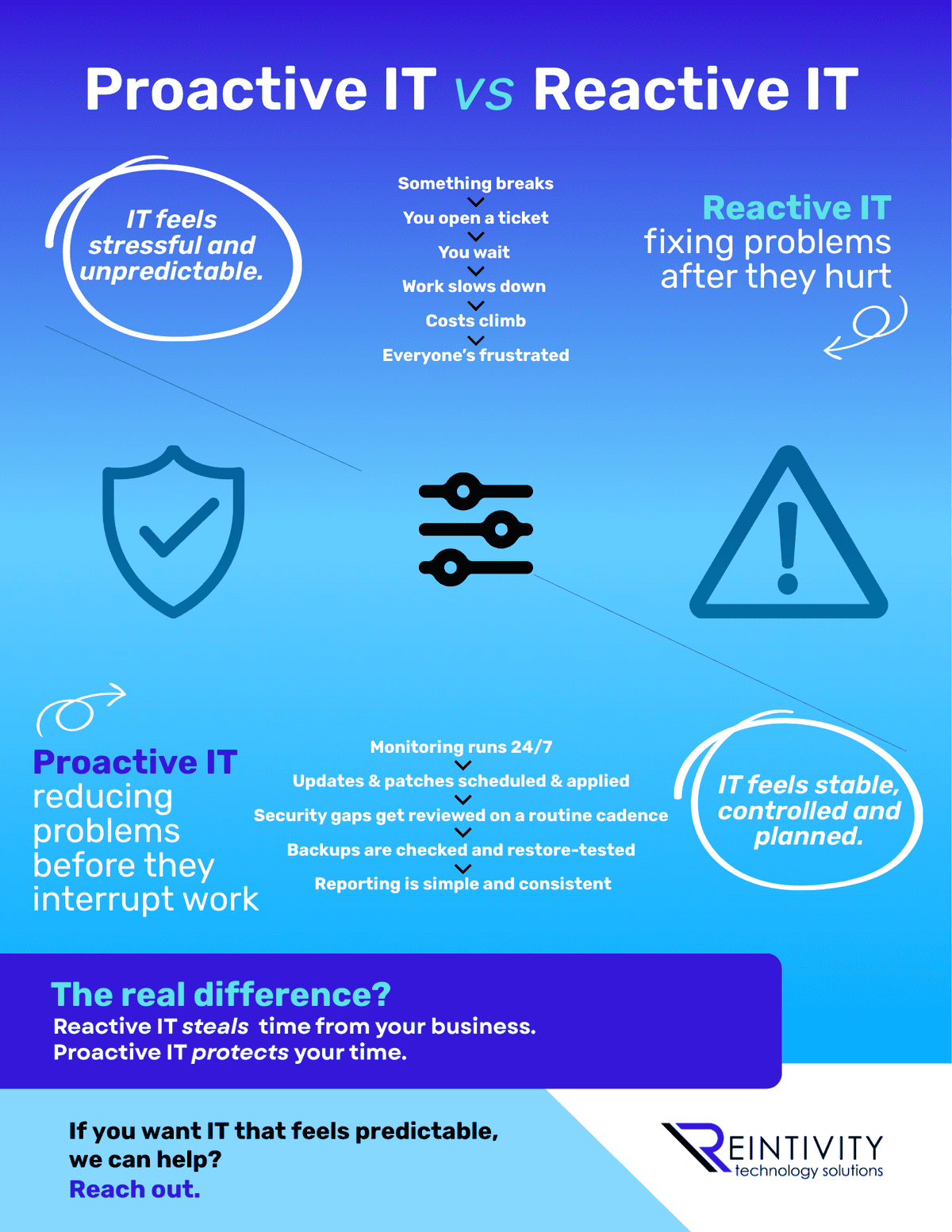
Proactive IT vs Reactive IT: Why It Feels So Different
Reactive IT is tickets, waiting, and surprise costs. Proactive IT is monitoring, patching, and tested backups. Which one are you running right now…

Understanding Illinois Laws That Affect AI Use in Business
Using AI in Illinois? HR tools, video interviews, biometrics, and marketing can trigger real laws. Here’s the plain-English map and what to fix first…
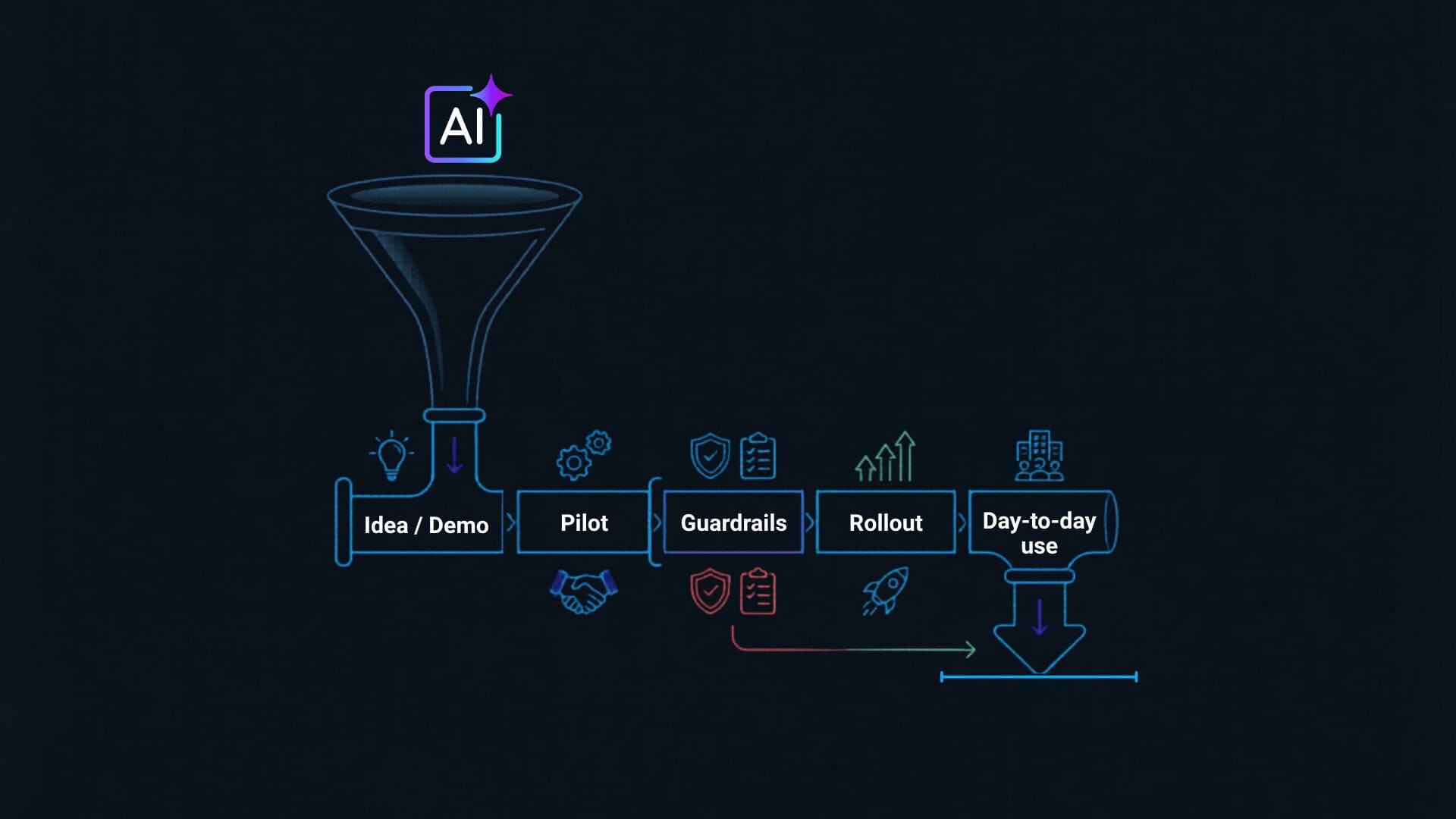
How to keep AI projects from stalling
AI pilots don’t fail from lack of budget. They stall from vague goals, weak guardrails, and unclear ownership. Three moves that get AI into daily work…
Let's get started
















