Digital fraud is faster and more convincing, often powered by AI. Reduce risk with a simple habit: stop, think, verify, plus MFA and better approvals before…
Operations & Support
MFA Without the Friction: A Practical Rollout Plan
MFA does not have to slow people down. Roll it out in the right order, pick low-friction methods, and cut login pain before it starts…
Ransomware Changed: It’s Not Just Lockouts Anymore
Ransomware isn’t just “systems down” anymore. Many attacks steal data first, then pressure you to pay. The fix starts with patching, visibility, and a plan…
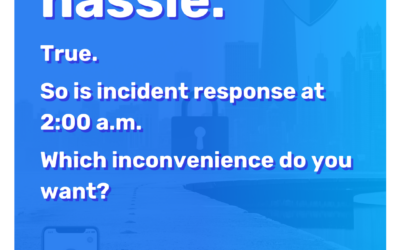
Stop Sending Mass Email From Your Primary Domain (and What to Do Instead)
Stop Campaign Email From Hurting Business Email....
Prepare your business for more refined cyberthreats
Cyberthreats are shifting from loud ransomware to quiet data theft and extortion. Reduce risk with patching, MFA, visibility, and a response plan before…
Two Small Teams Updates That Save Real Time
Teams is fixing two everyday chat frustrations: choose what Enter does, and forward up to five messages at once. If your Teams setup still feels messy…
Two small Microsoft Teams updates that make chat less frustrating
Two Teams fixes are finally here: choose what Enter does and forward multiple messages at once. Small changes, less daily friction, better chat flow when…
The 5-Question IT Check for Nonprofit Leaders
Before the next grant cycle, run this five-question tech check: roadmap, MFA or passkeys, device encryption, tested restores, and monitored alerts. If any answer is fuzzy…
The First Hour After a Cyber Incident: A Break-Glass Checklist
When an incident hits, confusion spreads fast. A short first-hour checklist helps your team contain damage, communicate clearly, and recover safely…
Technical Debt: The Silent Drag on Your IT Speed
Technical debt makes IT slower, riskier, and harder to manage. With Windows 10 support ended, here’s how to unwind it in phases without chaos…
Is “technical debt” slowing your business growth?
If IT feels slow, fragile, or harder to manage, technical debt may be the reason. With Windows 10 support ended, it’s time to reduce risk by…
What We Do: Consulting, Management & Sourcing
Need help improving your business processes and...
10 Things Attackers Hope Your Business Keeps Doing
Attackers count on small habits, not Hollywood hacks. See the 10 things they hope your business keeps doing and where to tighten up first…
AI Browsers at Work: Convenience vs Risk
AI browsers can save time, but may send what you view to the cloud. Before you approve them at work, set guardrails and train users to…
Consider this before using AI-enabled browsers at work
AI-enabled browsers can summarize and automate work, but they may also send sensitive on-screen data to the cloud. Before you roll them out, make sure…
Tech mistakes Chicagoland nonprofits can’t afford to ignore
If your nonprofit is running on workarounds, it is time to fix the fundamentals before the next outage, breach, or board question turns into…
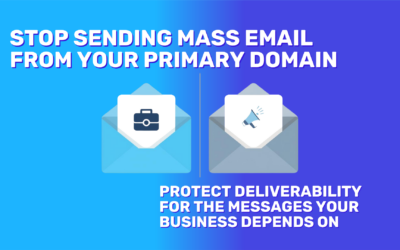
Human Firewall: The People-First Playbook for Blocking Phishing and Breaches
Most breaches start with a click—not a “hack.” Your best defense is trained people who spot the red flags and report fast. Here’s how to build that…
PowerPoint “Reuse Slides” Is Gone: Here’s the Workaround
If “Reuse Slides” vanished in PowerPoint, you’re not imagining it. Here are two quick ways to reuse slides and keep formatting mostly intact…
PowerPoint Removed “Reuse Slides” — Here’s the Fastest Clean Replacement Workflow
PowerPoint retired “Reuse Slides,” making deck reuse harder. Here’s the fastest drag-and-drop workflow to keep branding clean and save hours…
Edge Passkeys Now Sync Across Devices
Password resets burn time. Edge can now sync passkeys across devices, so your team signs in with face, fingerprint, or PIN and skips the reset loop…
When Your Tools Fight Back: The Friction Audit That Sets Up a Better Cloud Move
Most IT pain isn’t outages—it’s daily friction. Audit the drag, fix quick wins, then decide if cloud truly simplifies your next chapter…
Password resets are a tax. Passkeys are how we stop paying it.
Password resets are a tax. Passkeys can cut the bill—but only if they’re practical. Edge passkey sync removes a key objection, with a catch…
Ask Copilot: The Windows 11 Shortcut You Can Turn Off
Ask Copilot may land on your Windows 11 taskbar. Type what you need, and settings happen fast. It’s optional, and it could save your team…
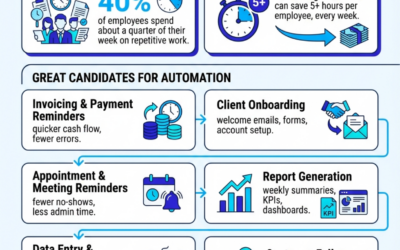
Busywork to Breakthrough: What to Automate First
Busywork is stealing your week. Automate the right workflows and save 5+ hours per employee—every week. Start with the best candidates and…
Windows Search is turning into a command bar for normal people
Windows Search is becoming a command bar. Ask Copilot turns “find” into “do”—and makes it an IT rollout decision, not a UI tweak…
Microsoft Edge just rolled out a new scam protection feature
Those “your computer is infected” pop-ups are evolving fast. Edge now blocks many of them automatically with AI, but only if you…
Firewall + Web Filtering: Stop Threats Before They Land
Your firewall checks traffic. Web filtering helps prevent risky clicks, fake login pages, and malware traps. Not sure yours matches today’s threats…
That Full-Screen “Virus Alert” Is a Scam: How Microsoft Edge Helps Stop Scareware
That full-screen “virus alert” isn’t your PC—it’s a webpage fishing for remote access. Here’s how Edge can shut it down before your team…
Your Firewall, Explained: What It Does, What It Misses, What to Check
Most leaders think “we have a firewall, so we’re fine.” But a firewall isn’t a babysitter—it’s a boundary. Here’s what it misses, and what to check…
Chicago Nonprofit Cyber Hygiene: Break Bad IT Habits & Reduce Wi-Fi Risk Without Breaking Your Budget
Chicago nonprofits: “free” Wi-Fi and small IT shortcuts can trigger big disruption. Break the bad habits, lock down the basics, and protect your mission…