Tools and Resources
eGuides
In-depth resources to navigate IT solutions
➤
How to
Short videos to get the most out of Microsoft
➤
Product Brochures
Learn about our solutions and offerings
➤
IT Pricing Calculator
Get an estimate for managed IT services
➤
Downtime Calculator
Estimate the cost of an outage event
➤
ROI Calculator
Estimate the return on your technology investment in minutes
➤
Password Strength Check
Test your password strength instantly
➤
Cyber Attack Awareness
Watch a hacker in action, stay protected
➤
Have I been Pwned
Check if your email or mobile was hacked
➤
Cyber Risk Score
Measure cybersecurity risk in minutes—fast, private, actionable
➤
Books
2 books to secure enhance and catapult your business into tomorrow
➤
IT Services Buyer's Guide
Key considerations before purchasing IT services
➤
Lastest Resources
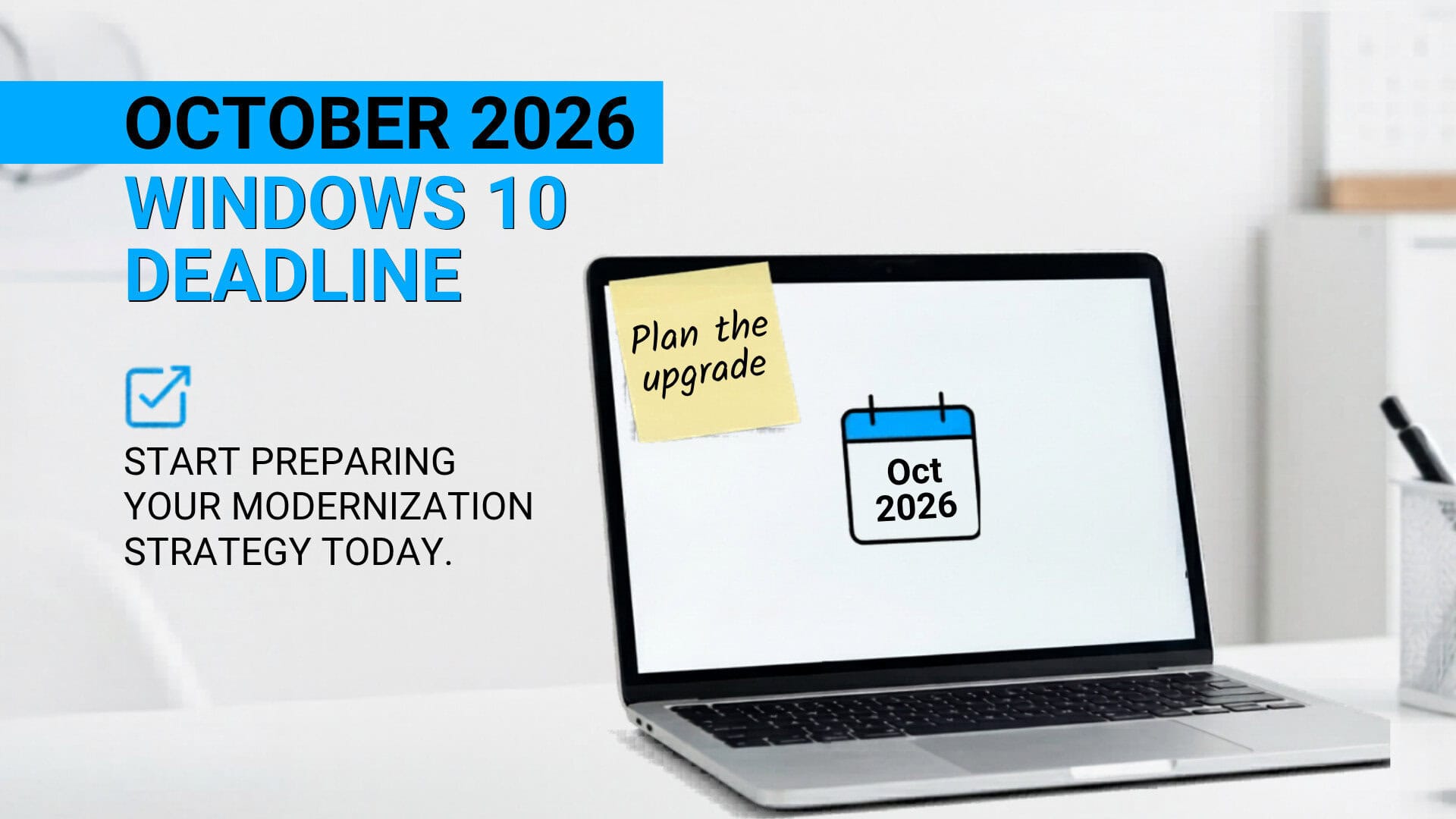
Relying on Windows 10 extended support? Your Chicago team needs an exit plan
Windows 10 ESU buys time, not safety. If your Chicago PCs are still on 10, use this quick plan to avoid a rushed Windows 11 scramble before…
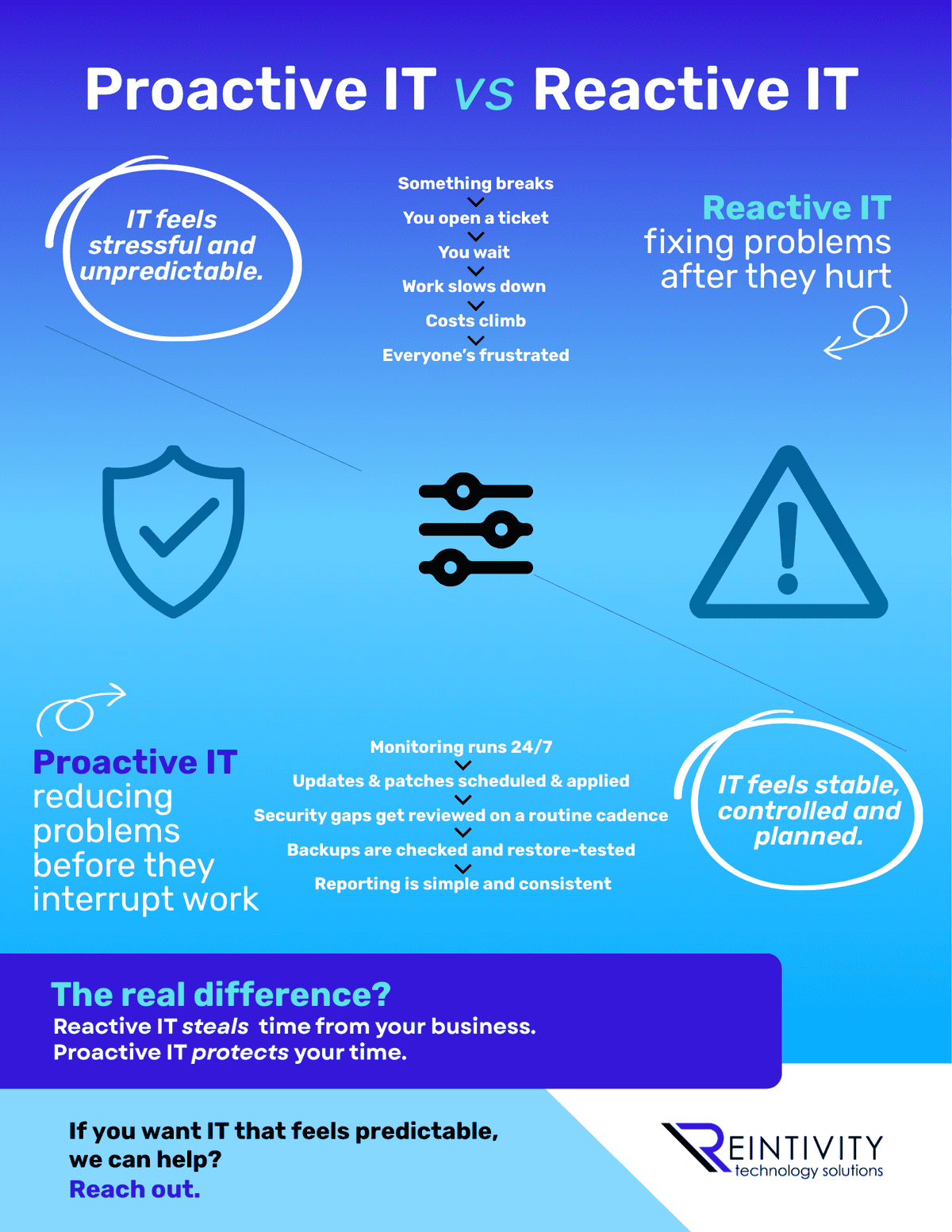
Proactive IT vs Reactive IT: Why It Feels So Different
Reactive IT is tickets, waiting, and surprise costs. Proactive IT is monitoring, patching, and tested backups. Which one are you running right now…

Understanding Illinois Laws That Affect AI Use in Business
Using AI in Illinois? HR tools, video interviews, biometrics, and marketing can trigger real laws. Here’s the plain-English map and what to fix first…
Let's get started